Education is a powerful tool for diversity. From Howard Zinn’s A People’s History of the United States, which tells narratives marginalized from most American history curricula, to using teach-ins as a form of education as activism, education plays an important role in building empathy and understanding that can promote greater diversity.
Teaching is not neutral
Recognizing that teaching isn’t neutral or unbiased is key to the understanding of education as reflective of diversity. Education inherently embodies an understanding of diversity that the educator has. Whether this educator is a teacher in a formal school, a conference facilitator, or even the media, their biases can work to make their classroom (in all different forms) an inclusive space or a space of marginalization.
Everyone learns differently
Bias in teaching is commonly discussed with the different ways people learn–the three cognitive types of learners: auditory, visual, and kinesthetic. Auditory learners gain information most effectively through listening and speaking activities. Visual learners prefer seeing or reading information. Kinesthetic learners learn by doing. An educator selects course learning activities that embody their own understanding of how people learn; this can be inclusive with activities from the varying learners types or marginalizing and focus on only one type of learner.
Because people tend to fit into multiple learning styles, teaching has adapted to incorporate different activities for different learning styles. Techniques such as active learning are being incorporated into lectures as a way to engage different types of learners and help students be more active. So even though everyone might be able to learn from a traditional lecture, it doesn’t mean that they learn most effectively that way, or that a lecture is creating an inclusive space of learning.
Education can marginalize voices
Recognizing education as an act of diversity means more than taking different learning styles into account. The topics that are discussed or omitted are also important. Omission of marginalized and non-elite narratives in the US history curriculum has been a critique from members of marginalized groups, like the rappers Tupac or Dead Prez, or American historians, like Howard Zinn.
Teaching and education are heavily steeped in social and cultural hierarchies. Paolo Freire brought to light how education can be used as a force of oppression (whether used by the ones with power, or the ones rebelling against the power) in his 1968 publication (first published in English in 1970), Pedagogy of the Oppressed. Education can play a role in keeping marginalized groups marginalized.
So, what can you do as an educator?
The role of an educator is not simply to overcome embedded oppressions, but to actively create an inclusive space of learning. By intentionally selecting various topics and being aware of how course design can marginalize voices is a good starting point.
It also includes structuring the course and assessments (if there are any) in a way that considers social diversity. When I was a graduate student instructor at the University of Minnesota, I had the pleasure of working with Katherine Brink who expanded my thoughts on how designing assessments can hinder students from learning, despite a desire to learn.
For example, time can be a barrier for students who are working part- or full-time and/or need to take care of family members while going to school. Requiring group work can be a burden to those without copious amounts of free time due, in part, to the difficulties of scheduling. As a conscious educator, you can structure group work and collaboration time during the class time to reduce the burden of logistics. Other factors, such as finances, family, and mental health, can all affect a learner’s performance. The course and its assessments need to take these into account as well.
The role of an educator is to create a space of radical inclusion. A space where each individual learner and their unique identities can not only be engaged, but flourish.
Education, Diversity, and the Digital
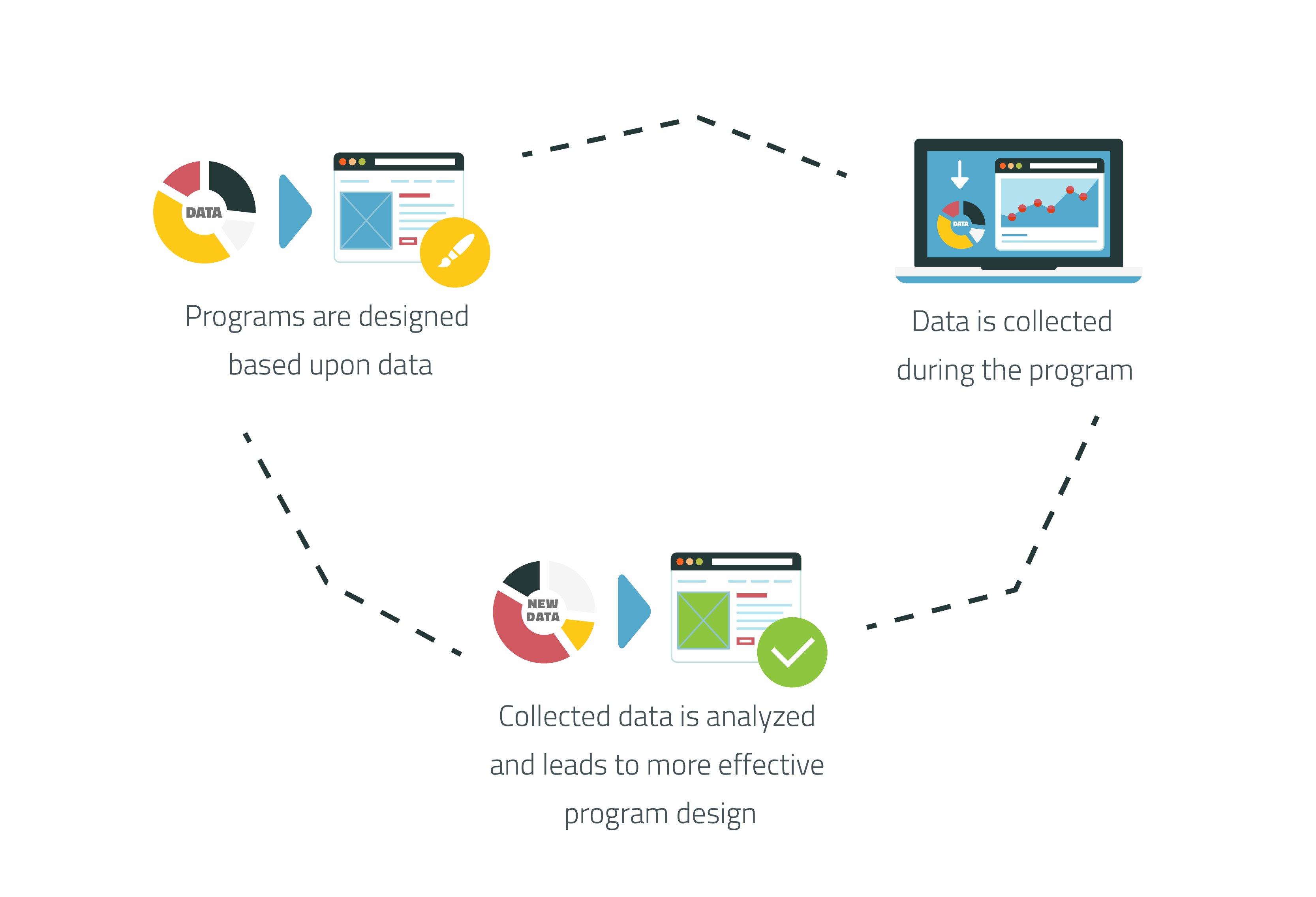
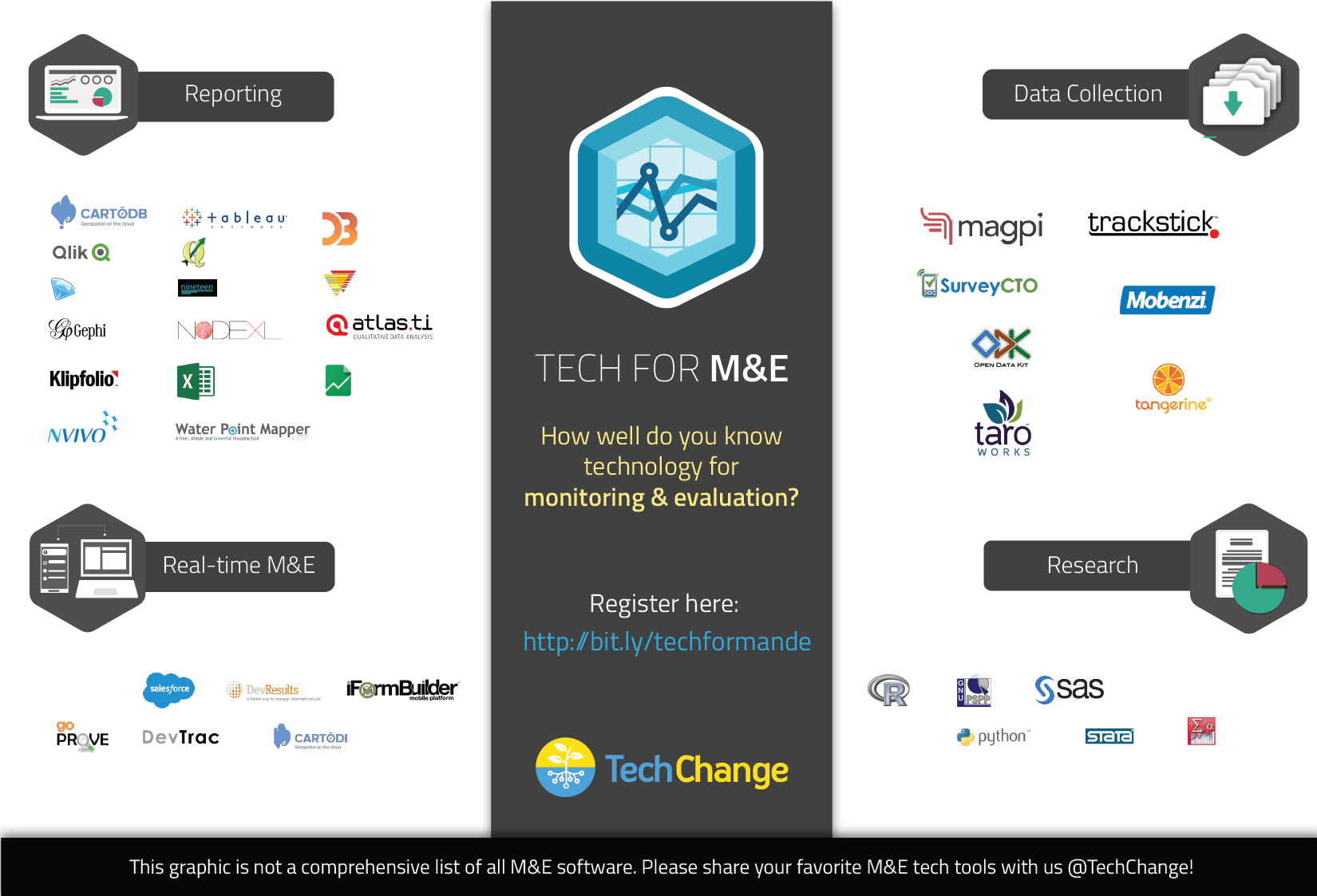
Technology has expanded the reach of education and the ‘classroom.’ Online courses bring together diverse group of learners from different cultural backgrounds and different educational systems into one learning environment.
Technology provides exciting new opportunities for collaboration and learning. But it also brings new forms of marginalization in the form of access to technology and affordable access to online data transfers. These are new hierarchies that educators in the digital age need to consider and help break down.
While I would love to offer concrete solutions and advice for digital educators, this is a new area that needs to be explored further. As we expand the reach of teaching, we need to remember that technology cannot replace a good educator.
What do you think about the role of education as a tool for diversity? Comment below or tweet at @NormanShamas or @TechChange!
This is the third post in our Digital Pedagogy series, where we will share how we are trying to make online social learning even better with new learning activities. Check out the previous posts here.